Configure a Classic connection
Configure a Classic connection when you have existing Direct Connect connections.
Step 1: Sign up for AWS
To use AWS Direct Connect, you need an account if you don't already have one.
Sign up for an AWS account
If you do not have an AWS account, complete the following steps to create one.
To sign up for an AWS account
- Open https://portal.aws.amazon.com/billing/signup .
- Follow the online instructions. Part of the sign-up procedure involves receiving a phone call and entering a verification code on the phone keypad. When you sign up for an AWS account, an AWS account root user is created. The root user has access to all AWS services and resources in the account. As a security best practice, assign administrative access to a user, and use only the root user to perform tasks that require root user access.
AWS sends you a confirmation email after the sign-up process is complete. At any time, you can view your current account activity and manage your account by going to https://aws.amazon.com/ and choosing My Account.
Create a user with administrative access
After you sign up for an AWS account, secure your AWS account root user, enable AWS IAM Identity Center, and create an administrative user so that you don't use the root user for everyday tasks.
Secure your AWS account root user
- Sign in to the AWS Management Console as the account owner by choosing Root user and entering your AWS account email address. On the next page, enter your password. For help signing in by using root user, see Signing in as the root user in the AWS Sign-In User Guide.
- Turn on multi-factor authentication (MFA) for your root user. For instructions, see Enable a virtual MFA device for your AWS account root user (console) in the IAM User Guide.
Create a user with administrative access
- Enable IAM Identity Center. For instructions, see Enabling AWS IAM Identity Center in the AWS IAM Identity Center User Guide.
- In IAM Identity Center, grant administrative access to a user. For a tutorial about using the IAM Identity Center directory as your identity source, see Configure user access with the default IAM Identity Center directory in the AWS IAM Identity Center User Guide.
Sign in as the user with administrative access
- To sign in with your IAM Identity Center user, use the sign-in URL that was sent to your email address when you created the IAM Identity Center user. For help signing in using an IAM Identity Center user, see Signing in to the AWS access portal in the AWS Sign-In User Guide.
Assign access to additional users
- In IAM Identity Center, create a permission set that follows the best practice of applying least-privilege permissions. For instructions, see Create a permission set in the AWS IAM Identity Center User Guide.
- Assign users to a group, and then assign single sign-on access to the group. For instructions, see Add groups in the AWS IAM Identity Center User Guide.
Step 2: Request an AWS Direct Connect dedicated connection
For dedicated connections, you can submit a connection request using the AWS Direct Connect console. For hosted connections, work with an AWS Direct Connect Partner to request a hosted connection. Ensure that you have the following information:
- The port speed that you require. You cannot change the port speed after you create the connection request.
- The AWS Direct Connect location at which the connection is to be terminated.
Note
You cannot use the AWS Direct Connect console to request a hosted connection. Instead, contact an AWS Direct Connect Partner, who can create a hosted connection for you, which you then accept. Skip the following procedure and go to Accept your hosted connection.
To create a new AWS Direct Connect connection
- Open the AWS Direct Connect console at https://console.aws.amazon.com/directconnect/v2/home .
- In the navigation pane choose Connections, and then choose Create a connection.
- Choose Classic.
- On the Create Connection pane, under Connection settings, do the following:
- For Name, enter a name for the connection.
- For Location, select the appropriate AWS Direct Connect location.
- If applicable, for Sub Location, choose the floor closest to you or your network provider. This option is only available if the location has meet-me rooms (MMRs) in multiple floors of the building.
- For Port Speed, choose the connection bandwidth.
- For On-premises, select Connect through an AWS Direct Connect partner when you use this connection to connect to your data center.
- For Service provider, select the AWS Direct Connect Partner. If you use a partner that is not in the list, select Other.
- If you selected Other for Service provider, for Name of other provider, enter the name of the partner that you use.
- (Optional) Add or remove a tag. [Add a tag] Choose Add tag and do the following:
- For Key, enter the key name.
- For Value, enter the key value.
[Remove a tag] Next to the tag, choose Remove tag.
It can take up to 72 hours for AWS to review your request and provision a port for your connection. During this time, you might receive an email with a request for more information about your use case or the specified location. The email is sent to the email address that you used when you signed up for AWS. You must respond within 7 days or the connection is deleted.
Accept your hosted connection
You must accept the hosted connection in the AWS Direct Connect console before you can create a virtual interface. This step only applies to hosted connections.
To accept a hosted virtual interface
- Open the AWS Direct Connect console at https://console.aws.amazon.com/directconnect/v2/home .
- In the navigation pane, choose Connections.
- Select the hosted connection, and then choose Accept. Choose Accept.
(Dedicated connection) Step 3: Download the LOA-CFA
After you request a connection, we make a Letter of Authorization and Connecting Facility Assignment (LOA-CFA) available to you to download, or emails you with a request for more information. The LOA-CFA is the authorization to connect to AWS, and is required by the colocation provider or your network provider to establish the cross-network connection (cross-connect).
To download the LOA-CFA
- Open the AWS Direct Connect console at https://console.aws.amazon.com/directconnect/v2/home .
- In the navigation pane, choose Connections.
- Select the connection and choose View Details.
- Choose Download LOA-CFA. The LOA-CFA is downloaded to your computer as a PDF file.
Note
If the link is not enabled, the LOA-CFA is not yet available for you to download. Check your email for a request for more information. If it's still unavailable, or you haven't received an email after 72 hours, contact AWS Support .
- If you're working with an AWS Direct Connect Partner or network provider, send them the LOA-CFA so that they can order a cross-connect for you at the AWS Direct Connect location. If they cannot order the cross-connect for you, you can contact the colocation provider directly.
- If you have equipment at the AWS Direct Connect location, contact the colocation provider to request a cross-network connection. You must be a customer of the colocation provider. You must also present them with the LOA-CFA that authorizes the connection to the AWS router, and the necessary information to connect to your network.
AWS Direct Connect locations that are listed as multiple sites (for example, Equinix DC1-DC6 & DC10-DC11) are set up as a campus. If your or your network provider’s equipment is located in any of these sites, you can request a cross-connect to your assigned port even if it resides in a different campus building.
Important
A campus is treated as a single AWS Direct Connect location. To achieve high availability, configure connections to different AWS Direct Connect locations.
If you or your network provider experience issues establishing a physical connection, see Troubleshooting layer 1 (physical) issues.
Step 4: Create a virtual interface
To begin using your AWS Direct Connect connection, you must create a virtual interface. You can create a private virtual interface to connect to your VPC. Or, you can create a public virtual interface to connect to public AWS services that aren't in a VPC. When you create a private virtual interface to a VPC, you need a private virtual interface for each VPC to which to connect. For example, you need three private virtual interfaces to connect to three VPCs.
Before you begin, ensure that you have the following information:
| Resource | Required information |
|---|
| Connection | The AWS Direct Connect connection or link aggregation group (LAG) for which you are creating the virtual interface. |
| Virtual interface name | A name for the virtual interface. |
| Virtual interface owner | If you're creating the virtual interface for another account, you need the AWS account ID of the other account. |
| (Private virtual interface only) Connection | For connecting to a VPC in the same AWS Region, you need the virtual private gateway for your VPC. The ASN for the Amazon side of the BGP session is inherited from the virtual private gateway. When you create a virtual private gateway, you can specify your own private ASN. Otherwise, Amazon provides a default ASN. For more information, see Create a Virtual Private Gateway in the Amazon VPC User Guide. For connecting to a VPC through a Direct Connect gateway, you need the Direct Connect gateway. For more information, see Direct Connect Gateways. |
| VLAN | A unique virtual local area network (VLAN) tag that's not already in use on your connection. The value must be between 1 and 4094 and must comply with the Ethernet 802.1Q standard. This tag is required for any traffic traversing the AWS Direct Connect connection. |
If you have a hosted connection, your AWS Direct Connect Partner provides this value. You can’t modify the value after you have created the virtual interface.
- (Public virtual interface only) You must specify unique public IPv4 addresses that you own. The value can be one of the following:
- A customer-owned IPv4 CIDR These can be any public IPs (customer-owned or provided by AWS), but the same subnet mask must be used for both your peer IP and the AWS router peer IP. For example, if you allocate a /31 range, such as 203.0.113.0/31 , you could use 203.0.113.0 for your peer IP and 203.0.113.1 for the AWS peer IP. Or, if you allocate a /24 range, such as 198.51.100.0/24 , you could use 198.51.100.10 for your peer IP and 198.51.100.20 for the AWS peer IP.
- An IP range owned by your AWS Direct Connect Partner or ISP, along with an LOA-CFA authorization
- An AWS-provided /31 CIDR. Contact AWS Support to request a public IPv4 CIDR (and provide a use case in your request)
Note
We cannot guarantee that we will be able to fulfill all requests for AWS-provided public IPv4 addresses.
- A public or private Border Gateway Protocol (BGP) Autonomous System Number (ASN) for your side of the BGP session. If you are using a public ASN, you must own it. If you are using a private ASN, you can set a custom ASN value. For a 16-bit ASN, the value must be in the 64512 to 65534 range. For a 32-bit ASN, the value must be in the 1 to 2147483647 range. Autonomous System (AS) prepending does not work if you use a private ASN for a public virtual interface.
- AWS enables MD5 by default. You cannot modify this option.
- An MD5 BGP authentication key. You can provide your own, or you can let Amazon generate one for you.
Public IPv4 routes or IPv6 routes to advertise over BGP. You must advertise at least one prefix using BGP, up to a maximum of 1,000 prefixes.
- IPv4: The IPv4 CIDR can overlap with another public IPv4 CIDR announced using AWS Direct Connect when either of the following is true:
- The CIDRs are from different AWS Regions. Make sure that you apply BGP community tags on the public prefixes.
- You use AS_PATH when you have a public ASN in an active/passive configuration.
We request additional information from you if your public prefixes or ASNs belong to an ISP or network carrier. This can be a document using an official company letterhead or an email from the company's domain name verifying that the network prefix/ASN may be used by you.
For private virtual interface and public virtual interfaces, the maximum transmission unit (MTU) of a network connection is the size, in bytes, of the largest permissible packet that can be passed over the connection. The MTU of a virtual private interface can be either 1500 or 9001 (jumbo frames). The MTU of a transit virtual interface can be either 1500 or 8500 (jumbo frames). You can specify the MTU when you create the interface or update it after you create it. Setting the MTU of a virtual interface to 8500 (jumbo frames) or 9001 (jumbo frames) can cause an update to the underlying physical connection if it wasn't updated to support jumbo frames. Updating the connection disrupts network connectivity for all virtual interfaces associated with the connection for up to 30 seconds. To check whether a connection or virtual interface supports jumbo frames, select it in the AWS Direct Connect console and find Jumbo Frame Capable on the Summary tab.
When you create a public virtual interface, it can take up to 72 hours for AWS to review and approve your request.
To provision a public virtual interface to non-VPC services
- Open the AWS Direct Connect console at https://console.aws.amazon.com/directconnect/v2/home .
- In the navigation pane, choose Virtual Interfaces.
- Choose Create virtual interface.
- Under Virtual interface type, for Type, choose Public.
- Under Public virtual interface settings, do the following:
- For Virtual interface name, enter a name for the virtual interface.
- For Connection, choose the Direct Connect connection that you want to use for this interface.
- For VLAN, enter the ID number for your virtual local area network (VLAN).
- For BGP ASN, enter the The Border Gateway Protocol Autonomous System Number of your on-premises peer router for the new virtual interface. The valid values are 1-2147483647.
- To configure an IPv4 BGP or an IPv6 peer, do the following: [IPv4] To configure an IPv4 BGP peer, choose IPv4 and do one of the following:
- To specify these IP addresses yourself, for Your router peer ip, enter the destination IPv4 CIDR address to which Amazon should send traffic.
- For Amazon router peer IP, enter the IPv4 CIDR address to use to send traffic to AWS.
[IPv6] To configure an IPv6 BGP peer, choose IPv6. The peer IPv6 addresses are automatically assigned from Amazon's pool of IPv6 addresses. You cannot specify custom IPv6 addresses.
- For Key, enter the key name.
- For Value, enter the key value.
[Remove a tag] Next to the tag, choose Remove tag.
To provision a private virtual interface to a VPC
- Open the AWS Direct Connect console at https://console.aws.amazon.com/directconnect/v2/home .
- In the navigation pane, choose Virtual Interfaces.
- Choose Create virtual interface.
- Under Virtual interface type, for Type, choose Private.
- Under Private virtual interface settings, do the following:
- For Virtual interface name, enter a name for the virtual interface.
- For Connection, choose the Direct Connect connection that you want to use for this interface.
- For Gateway type, choose Virtual private gateway, or Direct Connect gateway.
- For Virtual interface owner, choose Another AWS account, and then enter the AWS account.
- For Virtual private gateway, choose the virtual private gateway to use for this interface.
- For VLAN, enter the ID number for your virtual local area network (VLAN).
- For BGP ASN, enter the Border Gateway Protocol Autonomous System Number of your on-premises peer router for the new virtual interface. The valid values are 1 to 2147483647.
- To configure an IPv4 BGP or an IPv6 peer, do the following: [IPv4] To configure an IPv4 BGP peer, choose IPv4 and do one of the following:
- To specify these IP addresses yourself, for Your router peer ip, enter the destination IPv4 CIDR address to which Amazon should send traffic.
- For Amazon router peer ip, enter the IPv4 CIDR address to use to send traffic to AWS.
Important
If you let AWS auto-assign IPv4 addresses, a /29 CIDR will be allocated from 169.254.0.0/16 IPv4 Link-Local according to RFC 3927 for point-to-point connectivity. AWS does not recommend this option if you intend to use the customer router peer IP address as the source and/or destination for VPC traffic. Instead you should use RFC 1918 or other addressing, and specify the address yourself.
- For more information about RFC 1918, see Address Allocation for Private Internets .
- For more information about RFC 3927, see Dynamic Configuration of IPv4 Link-Local Addresses .
[IPv6] To configure an IPv6 BGP peer, choose IPv6. The peer IPv6 addresses are automatically assigned from Amazon's pool of IPv6 addresses. You cannot specify custom IPv6 addresses.
- For Key, enter the key name.
- For Value, enter the key value.
[Remove a tag] Next to the tag, choose Remove tag.
Step 5: Download the router configuration
After you have created a virtual interface for your AWS Direct Connect connection, you can download the router configuration file. The file contains the necessary commands to configure your router for use with your private or public virtual interface.
To download a router configuration
- Open the AWS Direct Connect console at https://console.aws.amazon.com/directconnect/v2/home .
- In the navigation pane, choose Virtual Interfaces.
- Select the connection and choose View Details.
- Choose Download router configuration.
- For Download router configuration, do the following:
- For Vendor, select the manufacturer of your router.
- For Platform, select the model of your router.
- For Software, select the software version for your router.
After you configure your router, the status of the virtual interface goes to UP . If the virtual interface remains down and you cannot ping the AWS Direct Connect device's peer IP address, see Troubleshooting layer 2 (data link) issues. If you can ping the peer IP address, see Troubleshooting layer 3/4 (Network/Transport) issues. If the BGP peering session is established but you cannot route traffic, see Troubleshooting routing issues.
Step 6: Verify your virtual interface
After you have established virtual interfaces to the AWS Cloud or to Amazon VPC, you can verify your AWS Direct Connect connection using the following procedures.
To verify your virtual interface connection to the AWS Cloud
- Run traceroute and verify that the AWS Direct Connect identifier is in the network trace.
To verify your virtual interface connection to Amazon VPC
- Using a pingable AMI, such as an Amazon Linux AMI, launch an EC2 instance into the VPC that is attached to your virtual private gateway. The Amazon Linux AMIs are available in the Quick Start tab when you use the instance launch wizard in the Amazon EC2 console. For more information, see Launch an Instance in the Amazon EC2 User Guide. Ensure that the security group that's associated with the instance includes a rule permitting inbound ICMP traffic (for the ping request).
- After the instance is running, get its private IPv4 address (for example, 10.0.0.4). The Amazon EC2 console displays the address as part of the instance details.
- Ping the private IPv4 address and get a response.
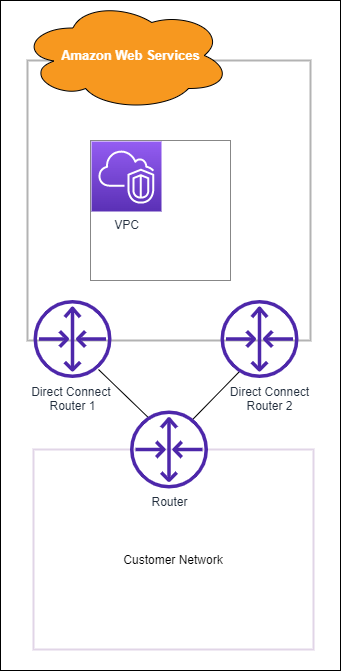
(Recommended) Step 7: Configure redundant connections
To provide for failover, we recommend that you request and configure two dedicated connections to AWS, as shown in the following figure. These connections can terminate on one or two routers in your network.
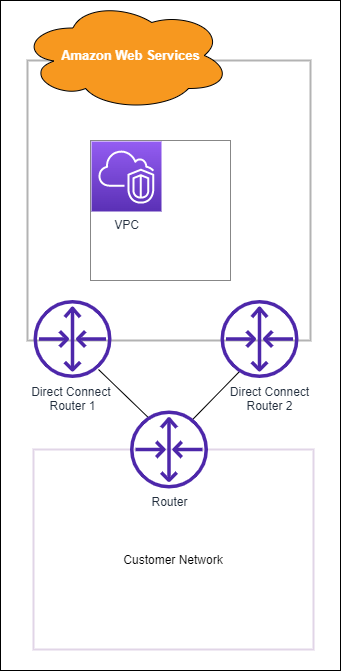
There are different configuration choices available when you provision two dedicated connections:
- Active/Active (BGP multipath). This is the default configuration, where both connections are active. AWS Direct Connect supports multipathing to multiple virtual interfaces within the same location, and traffic is load-shared between interfaces based on flow. If one connection becomes unavailable, all traffic is routed through the other connection.
- Active/Passive (failover). One connection is handling traffic, and the other is on standby. If the active connection becomes unavailable, all traffic is routed through the passive connection. You need to prepend the AS path to the routes on one of your links for that to be the passive link.
How you configure the connections doesn't affect redundancy, but it does affect the policies that determine how your data is routed over both connections. We recommend that you configure both connections as active.
If you use a VPN connection for redundancy, ensure that you implement a health check and failover mechanism. If you use either of the following configurations, then you need to check your route table routing to route to the new network interface.
- You use your own instances for routing, for example the instance is the firewall.
- You use your own instance that terminates a VPN connection.
To achieve high availability, we strongly recommend that you configure connections to different AWS Direct Connect locations.
For more information about AWS Direct Connect resiliency, see AWS Direct Connect Resiliency Recommendations .